Jfuscator
Protect Java software against code modification and IP theft.
Published by SecureTeam
Distributed by ComponentSource since 2010
Version: 6.6 Updated: Apr 18, 2019
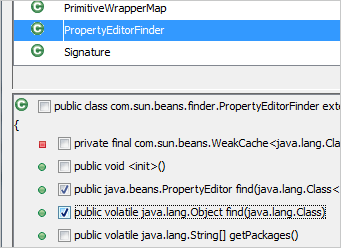
Jfuscator Protects more of your application than any other obfuscator because it knows what is safe to change and what needs to be left alone. Jfuscator automatically detects and modifies calls to reflection API to remain consistent with renamed symbols names.

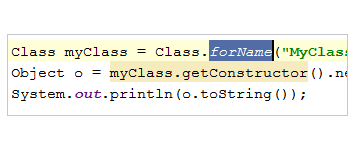
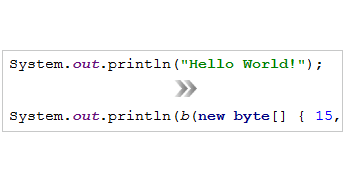
Morph strings that contain sensitive data, making an attack based on targeting encrypted strings impossible.

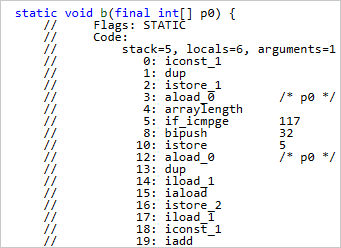
Break high level constructs such as loops, conditional and branching instructions by applying code transformations at byte code level. Jfuscator obscures program flow without changing what the code does at runtime.

Use the exclusions dialog to seamlessly avoid the renaming of unwanted classes, methods or fields.